Topic: security
ManageEngine enhances Log360 with features that improve the accuracy and precision of SIEM
ManageEngine introduced a dual-layered threat detection system in its security information and event management (SIEM) solution, Log360. This feature, part of Log360’s threat detection, investigation, and response (TDIR) component called Vigil IQ, aims to enhance the accuracy and precision of threat detection for security operations center (SOC) teams. The move is in response to challenges … continue reading
Palo Alto Networks updates Prisma SASE with enhancements to Zero Trust, user experience
Palo Alto Networks is introducing new updates to its platform that will help companies achieve Zero Trust security with its Prisma SASE application. Prisma SASE is a cloud-native architecture that integrates SD-WAN and security. “The strong force of distributed resources is shaping today’s organizations – workers are hybrid and applications are increasingly moving to the … continue reading
Report: 97% of consumers are bracing for cyberattacks to continue getting worse in 2024
Nearly all consumers are feeling like the number of cyberattacks that happen isn’t going down in the next year. Ninety-seven percent of respondents to a survey conducted by ThreatX said cyberattacks will either increase or remain the same in 2024, and 94% say that cyberattacks will be more difficult to defend against. In addition, 69% … continue reading
Frontegg launches Frontegg Forward for secure customer digital identity management
Frontegg, the provider of a customer identity and access management (CIAM) platform for modern SaaS apps, has unveiled Frontegg Forward, a platform expansion that revolutionizes how SaaS companies handle customer identity and user management. This expansion brings four key innovations to the forefront. Firstly, it provides an out-of-the-box solution for managing intricate hierarchies and organizational … continue reading
Trend Micro unveils new cloud container security capabilities
Trend Micro has introduced enhanced container security features for its main endpoint security platform, focusing on providing comprehensive protection, detection, and response for secure digital transformation. Trend Vision One Container Security’s capabilities allow analysts to expedite and improve incident prioritization, potentially reducing the time spent on container security incidents by up to two weeks, the … continue reading
Linkerd Enterprise launched as first enterprise-focused distribution of Linkerd Service Mesh Project
Buoyant, the company behind Linkerd, has introduced Linkerd Enterprise, a commercial distribution of Linkerd tailored for enterprise users. It enhances the open-source Linkerd with features specific to enterprise needs, such as zero trust and FIPS 140-2 compliance, a sophisticated cost-aware load balancer, automation for lifecycle management, and additional functionalities to support enterprise adoption. “Over the … continue reading
ITOps Times Open-Source Project of the Week: Cilium
Cilium provides eBPF-based networking, observability, and security for container workloads. It enables users to secure network connectivity between application services deployed using Linux container management platforms like Kubernetes. Cilium is built upon a Linux kernel technology known as eBPF. This technology allows for the real-time integration of robust security, visibility, and network control logic directly … continue reading
LogRhythm Axon quarterly release empowers security operations
LogRhythm announced a new release of its Axon solution that introduces significant enhancements and expansion to Axon and the full suite of LogRhythm solutions. The release enhances the capabilities of security operations centers by allowing seamless detection, investigation, and response to potential threats. LogRhythm Axon is a cloud-native SaaS platform with an interface that collects … continue reading
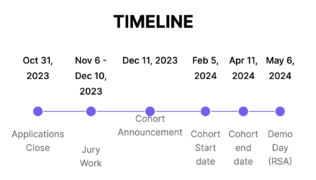
CrowdStrike and AWS announce startup accelerator for cloud native security companies
CrowdStrike has introduced the AWS & CrowdStrike Cybersecurity Startup Accelerator for EMEA-based startups. This accelerator program, part of AWS Startup Loft Accelerator, aims to support and nurture innovative cybersecurity startups in the region. It offers tailored mentorship, technical guidance, and partnership prospects. Additionally, promising early-stage cybersecurity firms may receive funding through CrowdStrike’s investment vehicle, the … continue reading
Cisco to acquire Splunk in effort to accelerate digital resilience
Cisco has announced its intention to acquire Splunk for approximately $28 billion in cash, at a rate of $157 per share. After the acquisition, Splunk’s CEO, Gary Steele, will join Cisco’s executive leadership team under the leadership of Chuck Robbins, who is currently chair and CEO of Cisco. Upon acquisition, Splunk and Cisco will be … continue reading
OneTrust’s latest update helps companies govern their AI programs
The security and trust intelligence company OneTrust has announced several new updates to enable its customers to build trust, manage and mitigate risks, and ensure compliance. “With the increase of importance in first-party data and use of AI, trust has quickly become the ultimate enabler for innovation,” said Blake Brannon, chief product and strategy officer … continue reading
SentinelOne launches new tool for simplifying incident management
SentinelOne is launching Singularity RemoteOps Forensics, a digital forensics product that helps companies of all sizes simplify incident response, making investigations and responses faster and more efficient. “As timelines for reporting and responding to breaches shrink, it is imperative that security teams have advanced forensics capabilities that make investigations faster and more efficient, and with … continue reading