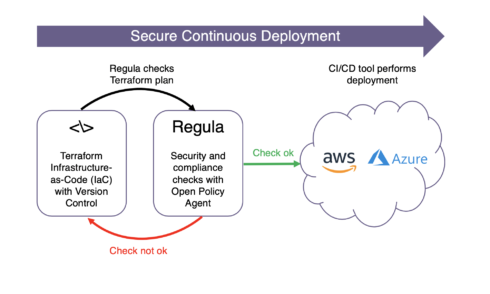
This week Fugue open sourced its Regula tool. Regula is a tool that evaluates Terraform infrastructure-as-code for security misconfigurations and compliance violations.
Development teams can integrate Regula into CI/CD pipelines to prevent cloud infrastructure deployments that could potentially have security or policy violations, Fugue explained.
RELATED OPEN-SOURCE PROJECTS:
Terraform | Tern | Project Calico
It can also be integrated with Fugue to provide end-to-end infrastructure security and compliance, though it can work independently of Fugue, too.
According to Regula’s GitHub page, there are two big parts to the project. The first is a shell script that generates a JSON-format terraform plan, which can then be consumed by Open Policy Agent. The second is a framework that merges resource info into a more accessible format, looks for rules and executes them, and creates a report with the results of all rules and a control mapping in the output.
“Developers design, build, and modify their own cloud infrastructure environments, and they increasingly own the security and compliance of that infrastructure,” said Josh Stella, co-founder and CTO of Fugue. “Fugue builds solutions that empower engineers operating in secure and regulated cloud environments, and Regula quickly and easily checks that their Terraform scripts don’t violate policy—before they deploy infrastructure.”