Topic: security
Qualys launches new solution for remediating threats efficiently
Security and compliance company Qualys has announced the launch of Qualys Custom Assessment and Remediation. This solution allows security teams to orchestrate workflows, secure applications, and take action to remediate threats. According to the company, traditionally when threats arise, typical responses include creating new processes and custom scripts that then need to be rolled out … continue reading
CSA releases guidelines for reducing security risk in healthcare
The Cloud Security Alliance (CSA) issued best practices for healthcare organizations to mitigate supply chain cyber risks in the Healthcare Supply Chain Cybersecurity Risk Management paper. “The move to the cloud and edge computing has expanded HDOs’ electronic perimeters, not only making it harder for them to secure their infrastructure but also making them more … continue reading
ITOps Times Open-Source Project of the Week: Starbase
This week’s ITOps Times open-source project of the week is Starbase, a tool that collects assets and relationships from services and systems including cloud infrastructure, SaaS applications, security controls, and more into an intuitive graph view backed by Neo4j. The tool enables users to integrate Neo4j with JupiterOne open-source data ingestion plugins to manage their … continue reading
Casting a light on shadow IT: Using a cloud access security broker
Given the increase in remote work and shadow IT usage, perhaps it shouldn’t be surprising that the cloud access security broker (CASB) market is exploding. Valued at $8.74 billion in 2020, the CASB market is projected to reach $32.9 billion by 2028—a projected compound annual growth rate of roughly 18% from 2021 to 2028. What … continue reading
Kyndryl expands partnership with Dell to address cyber attack threats
IT infrastructure provider Kyndryl announced an expansion of its global alliance with Dell Technologies that focuses on helping customers use data optimization, infrastructure management services, and a cyber resilience solution to protect their critical business assets. Kyndryl provides Cyber Incident Recovery with Dell Technologies to accelerate cyber resilience for customers using Dell’s high-performance storage, servers, … continue reading
Citrix Secure Private Access released to support flexible work models
The newly released Citrix Secure Private Access is a cloud-delivered, zero-trust network access offering that allows companies to provide employees access to apps and data that they need, from a variety of device types. “The IT pendulum has been swinging toward flexible work models for years, and the pandemic has accelerated the velocity,” said John … continue reading
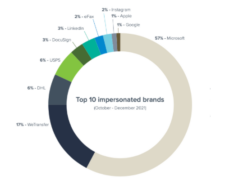
Report: Small businesses receive 350% more social engineering attacks than enterprises, mostly from Microsoft impersonators
An average employee of a small business with less than 100 employees will receive 350% more social engineering attacks than an employee of a larger enterprise. The most commonly impersonated brand is Microsoft, used by cybercriminals in 57% of phishing attacks – the most prevalent social engineering attack of 2021. These findings are from the … continue reading
ITOps Times Open-Source Project of the Week: Community Security Analytics
Community Security Analytics (CSA) is a set of open-sourced queries and rules designed by Google for self-service security analytics that are designed to help detect common cloud-based threats. Security Operations teams can use CSA to analyze Google Cloud logs to audit recent behavior and help detect threats to workloads. The queries are mapped to the … continue reading
Red Hat OpenShift 4.10 released
The new Red Hat OpenShift 4.10 release is based on Kubernetes 1.23 with the CRI-O 1.23 runtime and offers new enhancements and features for both developers and administrators. Among the 45 enhancements are the ability to change static network configurations after cluster deployment with enhanced networking metrics and debuggability. OpenShift also provides a way to … continue reading
Context-aware detections available in Google Chronicle
Google announced the public preview of context-aware threat detections, alert prioritization, and risk scoring on Google Chronicle, which is a solution for threat detection. The new capability aims to help security professionals create efficiencies in customers’ threat detection and response. “An alert in isolation does not provide sufficient information, and associated metadata, context, and asset … continue reading
Google Cloud acquires Mandiant for $5.4 billion
Google entered into a definitive agreement to acquire threat intelligence provider Mandiant for approximately $5.4 billion. Upon the close of the acquisition, Mandiant will join Google Cloud. Mandiant gathers research from more than 300 intelligence analysts to power its dynamic cyber defense solutions that are delivered through the managed multi-vendor XDR platform, Mandiant Advantage. Together … continue reading
DENT 2.0 released
DENT 2.0 is now available with new features that can be utilized by distributed enterprises in retail and remote facilities. The DENT project is an open-source network that uses the Linux Kernel, Switchdev, and other Linux-based projects. DENT was launched in December 2019 under the umbrella of the Linux Foundation with the aim to simplify … continue reading