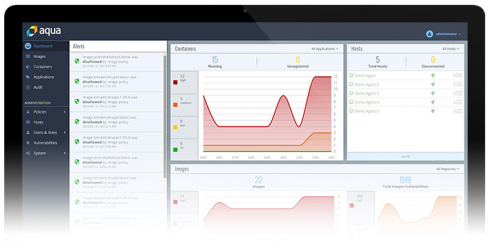
Cloud-native and containerized application security provider Aqua Security is introducing 3.2 of its Aqua Container Security Platform this week. The latest release comes with new capabilities for full-stack and serverless security, updated compliance features, and an OS-level security profile automation tool.
“Sophisticated attacks often exploit unknown vulnerabilities in the application or operating system, also known as ‘zero days,’ to either escalate privileges, run arbitrary code, or exfiltrate data,” the company wrote in the announcement. “Doing this at the OS level requires the use of system calls (syscalls), core functions that applications use to request the OS perform anything from opening files, creating network connections, to rebooting the system.”
To reduce the attack surface presented by the more than 330 syscalls the company said are available for container operation at the OS level, the Aqua Container Security Platform is implementing Linux community-developed seccomp profiles, which allow for disabling any syscalls unnecessary to the operation of a container. In addition, Aqua has taken extra steps in version 3.2 of the platform to make security at the syscall level easier to implement for the average developer, the company explained.
“Docker, for example, has disabled 50 syscalls in its default seccomp profile for running Docker containers,” the company wrote. “However, this still leaves more than 250 syscalls enabled, most of which would not be necessary for a specific application, and best practices are for developers to disable them. The challenge is that creating custom profiles for an application is difficult because it requires a deep low-level understanding of how the application uses syscalls — which is why most organizations often rely on the weak default.”
With the new release, Aqua is incorporating a profiler to analyze a container’s syscall use to automatically write up a seccomp profile that only allows for necessary syscalls, of which there are typically only 40-70 in use by a container, the company said, “reducing the attack surface by as much as 90 percent.” Users will be alerted in the event that a blacklisted syscall sees an attempted use, which will be blocked automatically by Aqua.
“Aqua is committed to making cloud-native applications more secure while minimizing any disruption to business continuity,” Amir Jerbi, CTO and co-founder of Aqua Security, said in the announcement. “Dynamically profiling system calls is the kind of modern application security we can enable with containers that was difficult to do well with monolithic applications, providing a fully automated and accurate method of blocking malicious activity and preventing exploits.”
In addition, the company said it is broadening the scope of its container security with added serverless infrastructure security features like hard-coded secrets and malware scanning for AWS Lambda, runtime protection controls for CRI-O and containerd, and “Thin OS” protections, which monitor hosts for successful and failed logins.
Compliance updates include Aqua Container Firewall’s ability to use domain and IP-specific rules, out-of-the box templates for developers to meet NIST, PCI, HIPAA and GDPR requirements, Azure Container Registry quarantine integration and Federated Single Sign-On from Microsoft ADFS, Okta and Google Apps among others with enhanced SAML support.